It can be challenging to isolate specific functionalities and test them due to complex dependencies, integrations, and architectures. So, to identify potential risk areas and crucial integration points, testers have to carry out an in-depth analysis of the technical intricacies of a system. While following the dynamic approach, software execution is about observing and evaluating its performance and behavior. The primary focus is on validating the non-functional and functional aspects of software through the active execution of test cases. A process or standard-compliant testing approach adheres to pre-defined frameworks, standards, and processes to facilitate compliant and consistent testing practices. It also takes different factors such as test efficiency, risk prioritization, and functional coverage into consideration, simultaneously minimizing unnecessary or redundant test cases.
- The respondents are asked the same set of follow-up questions for each concept to get further insights.
- Whether the development approach is Waterfall or Agile, it’s always a good practice to adapt to the test approach accordingly.
- Researchers can ask follow-up questions about the various attributes of a concept, such as what they liked about the concept, it’s look and feel, price point, etc.
- They include data models, behavioral models, functional models, and so on.
As a result, project teams can deliver robust and reliable software that meets all business requirements and user expectations. A reactive testing approach involves test design that comes after developing the software. Teams usually focus on identifying and taking care of defects after they are apparent or have already occurred. This approach usually comes into the picture when the involvement of testers during early software development stages is limited. Primary testing activities occur after the development phase is over, as testers receive either partially or fully completed software for functionality validation. Test approach also offers test execution guidelines, test automation, and test data management, which makes managing tests more efficient.
Consultative Approaches
Although, keep in mind that your automated test suites should be maintainable and robust. Some tasks that you can easily automate to save effort and time include result analysis, test execution, and data generation. The most important thing is to perform regular reviews and updates on automated test scripts to keep on par with evolutionary systems.
Such assessments help identify any constraints or resource gaps upfront, making room for proactive redressal measures. It also allows testers to create appropriate timelines and realistic schedules, which further contributes to executing a productive testing approach and optimizing available resources. A thorough assessment of resource requirements is a must to enable effective planning, resource allocation, and test management. A pragmatic and fruitful test approach can only result from a clear understanding of the resources required, such as test tools, skills, number of testers, test environments, etc. Test design is the process involving creating test scripts and test cases based on defined test requirements and objectives. The team members systematically identify test conditions, specify expected outcomes, define input data, and determine test execution steps.
Examples of consultation
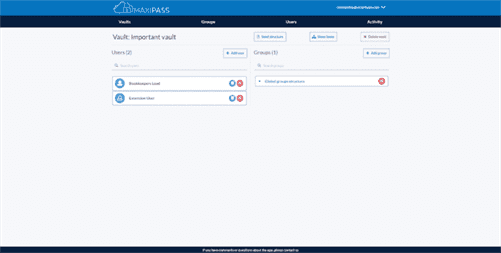
Here are some of the most common test approach challenges and how you can easily overcome them. To avoid confusion while deciding on a test approach or strategy, it’s important to consider a list of definition of consultative different factors while making a choice. Testing driven by the advice and guidance of appropriate experts from outside the test team (for example, technology experts and/or business domain experts).

It involves inputting different values as a method of assessing responses. Dynamic testing also encompasses techniques like acceptance testing, system testing, integration testing, and unit testing. The core aim here is to uncover errors, defects, and software vulnerabilities and make room for iterative improvements along with some real-time feedback. This process also involves assigning priority to different activities, outlining employee roles, and identifying dependencies.
Every technique offers users a distinct approach to assessing system performance, verifying functionality, and uncovering different types of defects. While following a proactive testing approach, testers design tests in the earlier phases of the testing cycle to identify and fix defects. It emphasizes the continuous involvement of the team from the starting phases of the Software Development Life Cycle to recognize and fix potential bottlenecks and possible risks. It follows the concept that prevention is better than cure instead of solely detecting and resolving issues. It’s important to establish the testing scope and boundaries to develop an effective and highly-focused testing approach. It defines the extent and restrictions of different testing activities, which ensures manageable and well-defined testing efforts.

The more dynamic product development becomes, the more flexible you have to be. Transitions between different components of a project are going to happen all the time. So, to keep these transitions smooth and hassle-free, there has to be a stable communication network among team members. This practice will make the entire test approach less error-prone and increase the convenience with which different processes operate. If documentation is compromised, the choice of testing techniques would be somewhat limited, and there would also be major confusion.

Considering the neverending list of testing activities, it’s always a good idea to create a comprehensive and detailed plan, also known as carrying out a test plan. It includes defining the objective and scope of testing, recognizing deliverables, estimating timelines and resources, and analyzing the test environment as well as requirements for test data. There are several instances where testers have to optimize their efforts within limited resources and time frames. As a result, testing activities tend to become compressed, risk inadequacies prevail, and test coverage compromises due to tight project deadlines. Prioritizing test efforts on the basis of risk-prone areas and critical functionalities can come in handy. A consultative test approach is an inclusive and collaborative testing approach that focuses on active stakeholder engagement throughout the STLC.
Testers usually conduct testing in a controlled and structured manner which ensures the auditability, reproducibility, and traceability of various activities. This approach enables consistent and efficient testing compliant with established norms. Implementing a reactive testing approach often occurs when there are constraints on resources and time. However, it can lead to increased maintenance costs since testers detect defects at a later stage in the Software Development Life Cycle.